Rules to Better Cloud Security - 4 Rules
To enhance your cloud security, manage your Azure Security posture effectively by utilizing Azure Security Center's alerting features. Regularly review your security posture to identify and mitigate potential risks, ensuring your cloud environment remains secure.
Effective management of Microsoft Entra ID (formerly Azure Active Directory) is crucial for maintaining the security and efficiency of your organisation's IT infrastructure. Neglecting best practices can lead to unauthorised access, data breaches, and operational disruptions.
1. Enforce Strong Authentication
- Implement Multi-Factor Authentication (MFA): Require MFA for all users, especially administrators, to add an extra layer of security.
- Adopt Passwordless Authentication: Utilise methods like Windows Hello for Business or FIDO2 security keys to enhance security and user experience.
2. Apply the Principle of Least Privilege
- Use Role-Based Access Control (RBAC): Assign users the minimum permissions necessary for their roles to reduce the risk of unauthorised access.
- Implement Just-In-Time Access: Utilise Privileged Identity Management (PIM) to grant temporary access to resources only when needed.
3. Regularly Review and Audit Access
- Conduct Access Reviews: Periodically review user access to ensure that only authorised individuals have access to resources.
- Monitor Sign-In Activity: Keep track of user sign-ins to detect unusual or suspicious activities promptly.
4. Secure Application Registrations
- Use Certificates Over Secrets: Always use certificate credentials for app authentication instead of client secrets, as certificates are more secure.
- Limit API Permissions: Assign the least privileged permissions necessary for applications to function.
5. Enable Security Features
- Activate Security Defaults: Enable security defaults in Microsoft Entra ID to enforce a basic level of security across your organisation.
- Implement Conditional Access Policies: Define policies that grant or block access based on conditions like user location, device state, or risk level.
6. Plan for Emergency Access
- Create Break Glass Accounts: Establish at least two emergency access accounts that are not protected by MFA to ensure access during critical situations.
- Monitor and Secure Emergency Accounts: Regularly audit these accounts to ensure they are not misused and are only accessed during emergencies.
7. Use Clear Access Group Naming Conventions
Clear and consistent naming conventions for access groups make management simpler and ensure clarity across the organisation.
why are naming conventions important?
Without clear naming conventions, it becomes difficult to understand the purpose or scope of access groups, leading to confusion and potential security risks.
best practices
-
Follow a Standard Structure: Include key details in the group name, such as department, function, and access level.
- Example:
[Department]-[Resource]-[Level] HR-Payroll-ReadOnlyorIT-SharePoint-Admin
- Example:
-
Use Prefixes for Type Indication: Add a prefix to indicate the type of group.
DL-for Distribution List,SEC-for Security Group,O365-for Office 365 Group 'Intune-' for Intune policies.
- Avoid Ambiguity: Ensure names are descriptive but concise. Avoid generic terms like "Admin" or "Users" that lack specific context.
- Adopt Case Conventions: Use consistent casing, such as PascalCase or lowercase, for easy readability. SSW uses kebab case :)
Common Naming Conventions Example
Name Purpose SEC-IT-VPN-Access Provides VPN access for IT personnel. SEC-Marketing-WebAnalytics Grants access to web analytics tools. SEC-Finance-ERP-ReadOnly Read-only access to the ERP system. O365-SharePoint-Accounts-private-library-ReadWrite Read-write access to the Accounts SharePoint library. DL-All-Company-Broadcast Organization-wide communication group. Intune-User-AccountingSoftware Intune user policy to install accounting software Intune-Computer-ScreenTimeout Intune computer screen timeout policy Figure: Good examples of access group naming conventions that improve clarity and reduce errors in assignment.
By adhering to these best practices, including clear naming conventions for access groups, you can strengthen your organization's security posture and streamline the management of Microsoft Entra ID.
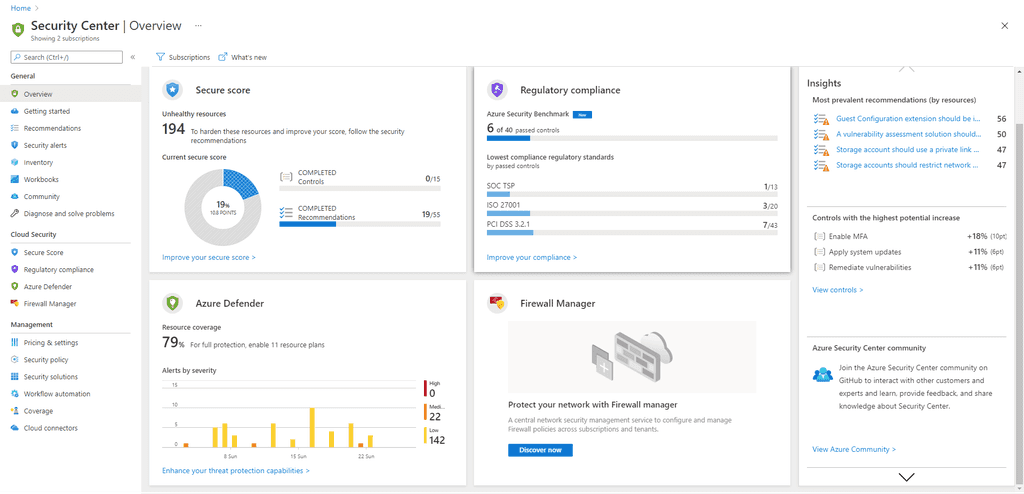
Azure Security Center is a fantastic way to start improving the security of your Azure environment. To be able to see any of the information Azure Security Center can provide, you'll need to follow Azure Security Center permissions guidelines.
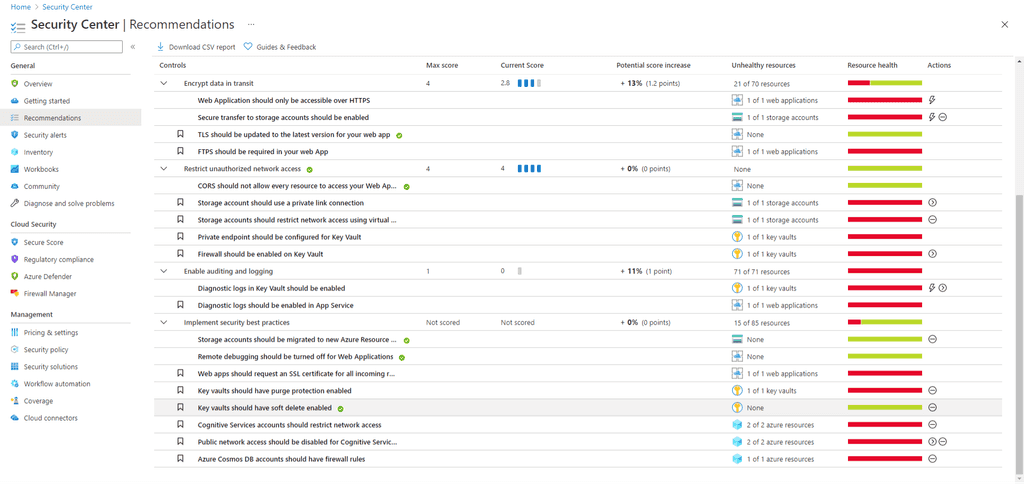
The Secure Score provides a way to easily identify which things are of greater importance and to help work methodically to improve security.
A lot of the recommendations are very simple to rectify, often it takes very little effort to make significant improvements.
Note: Remember though, that only you as the application developer can know how sensitive the data you are handling is.
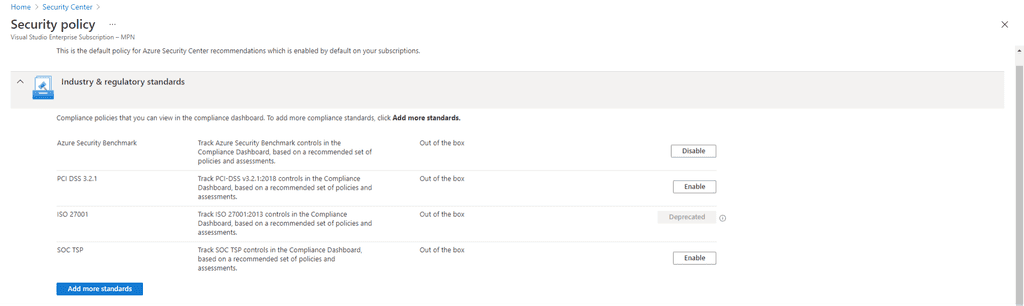
If you are working with a system that must comply with a regulatory framework around data protection, Azure Security Center allows turning on security policies covering many of the most common regulatory frameworks. PCI DSS 3.2.1, ISO 27001 and SOC TSP are all available, and there's a long list of others.
Once your environment is secured sufficiently you need to configure some alerting.This will ensure that any changes either due to changes in your Azure deployment or more importantly improved scanning in Security Center result in you being alerted so that your infrastructure can be better secured.
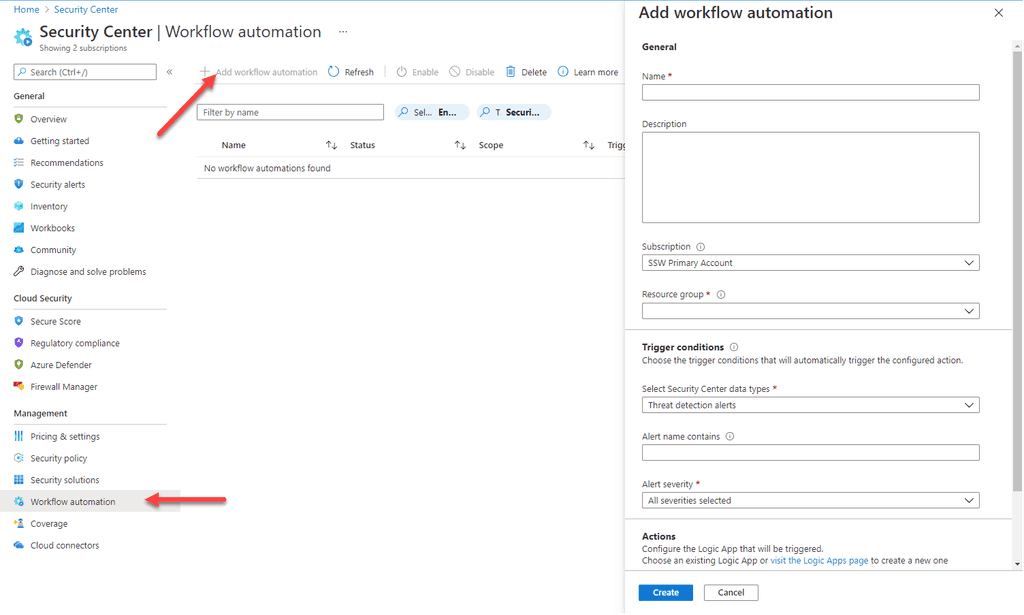
Figure: To configure alerting try this You can then set up the Action to notify you. There're all sorts of filtering functionality as well.
Set up alerting on at least the Security Center recommendations and Threat Detection alerts. If you need to comply with a regulatory framework, then it's important to add an alert for that too (this is the 3rd of the Security Center data types), so that you can avoid compliance failures.
As things change, you should schedule a regular review of security posture. This should involve reviewing whether the current policy is appropriate. Consider the following:
- Whether there are any outstanding alerts
- Changes in the nature of the data you are storing that might require further policy adjustment
- Compliance is now required with a new regulatory framework
- How regularly this should be reviewed (quarterly is recommended)